QR Codes for Authentication: How Secure Access Works

Fast access should feel simple, not shaky. Businesses need authentication that protects accounts, apps, devices, workspaces, and sensitive actions while helping people move fast. A QR Code can make that moment feel effortless by bridging the gap between devices: Scan, confirm, enter.
QR Codes for authentication can support multi-factor authentication, contactless login, passwordless access, and identity verification across SaaS dashboards, shared tablets, kiosks, front desks, and events. The QR Code starts the journey, but expiration rules, device checks, session matching, and clear prompts create trust while preventing unauthorized access. Teams can first explore how QR Codes are generated, then design the best protocol for what happens after the scan.
This guide keeps the focus practical. You will see how QR Code authentication works, where it fits best, and how teams can pair simple scanning with smart security controls.
Note: The brands and examples discussed below were found during our online research for this article.
Key takeaways
- QR Code authentication helps verify identity by letting someone scan a code that starts or approves a secure access flow. The QR Code is only one part of the process; the real protection comes from the time limits, device checks, and session controls behind it.
- Businesses can use QR Codes for authentication in several ways, including 2FA, passwordless sign-in, contactless login, and identity verification. The best approach depends on the user journey, the level of risk, and whether the scan reduces friction in a meaningful way.
- Dynamic QR Codes are often a stronger fit for authentication than static ones because they support short-lived, session-based access.
- Strong implementations balance usability and trust: QR Code authentication works best when it includes secure destinations, expiration controls, trusted-device checks, and clear prompts.
What is QR Code authentication?
QR Code authentication uses a scannable 2D barcode to help confirm someone’s identity or authorize access to a system, account, session, device, location, or action. The workflow moves verification to a trusted Android, Microsoft, or iOS smartphone, app, badge, or secure confirmation page.
A standard quick-response (QR) Code scan might open a menu. Authentication adds a security step. The scan starts the authentication process, but the user still needs a trusted device, an active account session, a biometric check, SMS one-time passwords, or another form of proof to validate their identity.
Three ideas matter here: Authentication confirms who the user is. Authorization decides what the user can access. Login brings the user into the system. A QR Code can support one step or connect all three, such as when used on a desktop login screen, for trusted phone approval, and for access to the right workspace.
How QR Code authentication works
Picture a user who wants to open a SaaS dashboard on a laptop. The login page shows a QR Code. The user scans it with a trusted mobile app. The phone shows the app name, device type, or session details. The user approves the request with a tap or biometric check, enabling real-time authorization. The system checks the request, matches the session, and opens the dashboard.
The QR Code usually carries a session reference, a secure token request, or short-lived authentication data via secure encoding, not a permanent password or a reusable credential. Strong authentication systems treat the code as a doorway to a controlled process, not as the key to the whole building.
Generate, scan, verify, and grant access
A strong flow follows four steps. First, the system generates a temporary, unique QR Code for one session or login attempt. Second, a user scans it with a trusted mobile device or a dedicated authenticator app. Third, the system checks expiration, session matching, and other proof, such as biometrics, device trust, or a one-time code. Fourth, the system grants access, blocks the request, or gives a clear next step.
Dynamic QR Codes fit this model because they support time-sensitive, session-specific destinations instead of static links that linger.
Where QR Codes fit into authentication flows
QR Codes can improve several access experiences when teams and identity providers match the scan to the right risk level and user moment, complementing traditional authentication methods.
Two-factor authentication
QR Codes can add a second confirmation step after the first login action. A user enters a username on a laptop, then scans a QR Code with a trusted phone to approve the session. That flow raises confidence without code copying. For higher-risk actions, teams can add biometrics or a one-time code after the scan to strengthen the MFA layer.
Passwordless and contactless login
Some workflows use QR Codes to reduce or remove password entry, facilitating a smooth passwordless authentication experience. A user can sign in to a desktop app from a phone session, authenticate on a kiosk without typing credentials, or access a shared workstation without leaving password traces on the keyboard. Teams still need device checks, identity proof, expiration rules, and fallback options.
Identity verification and approval flows
QR Codes can verify identity outside a traditional account login. They can support visitor check-in, secure device pairing, event access, contractor entry, or approval for a sensitive action. The scan guides the user into a focused confirmation step without long forms or manual handoffs.
Common use cases for QR Code authentication
The best use cases combine a clear user need with a smart security layer. Enterprise and SaaS teams often see big gains because they manage many users, devices, and access levels. The right QR Code solutions give operators speed, users clarity, and security teams a cleaner audit trail.
Support shared devices and workplace access
Healthcare, retail, manufacturing, logistics, hospitality, and field teams often rely on shared tablets, kiosks, scanners, or workstations. Manual login slows everyone down. Long passwords frustrate frontline teams. Shared credentials create risk. QR Code authentication can help employees move into the right session faster: Scan with a trusted device or badge app and start the shift. The system can end the session after a timeout, a role change, or a logout, giving admins greater control than shared password setups offer.
Simplify SaaS login across desktop and mobile
SaaS users often already trust their phones through an authenticated mobile app, biometric unlock, or managed profile. QR-based login lets a desktop screen hand the secure step to that trusted phone. The result feels familiar: Scan, approve, enter. Users avoid password fatigue, teams reduce drop-off, and support teams handle fewer reset requests. For marketers and product teams, this flow can turn authentication from a conversion speed bump into a polished brand moment and a superior user experience.
Manage visitor access and temporary entry
Guests, contractors, event attendees, and temporary workers need access, but they rarely need long-term credentials. QR Codes can guide them into short-lived check-in, Wi-Fi, building access, or event verification flows. A visitor can scan at the front desk, confirm details, and receive next steps. An attendee can scan at entry and move through the line faster. A contractor can access only the tools that match the job window.
What makes QR Code authentication secure
QR Code authentication does not create safety or risk by itself. The workflow design decides the outcome. A strong setup protects the destination, limits the lifespan, checks users and devices, monitors sessions, and explains the actions it takes to mitigate potential security risks.
User education matters because attackers abuse trust in scans, often employing phishing tactics to steal credentials. Teams that ask “Are QR Codes safe?” should look beyond the image and evaluate the destination and controls. They should also train users to spot quishing risks and other security threats, where attackers use QR Codes to lure people to fraudulent destinations.
Dynamic QR Codes and short expiration windows
Dynamic QR Codes often fit authentication because systems can create them for a specific moment. A code can point to a session that expires in seconds or minutes. It can stop working after one scan, one approval, or one failed attempt. Short windows reduce reuse and tie each scan to the exact login or verification request.
Trusted-device checks and extra verification
A scan alone may not prove enough for high-risk access. Strong flows pair the scan with another form of proof. The system can check whether the phone belongs to a known user, whether the device meets company policy, whether the app session remains valid, and whether the user can pass another challenge.
Session controls and monitoring
Authentication should continue to work after the scan. Admins need tools that manage the session from start to finish. One-time use, automatic expiration, logout triggers, revocation, and activity logs all help teams control access after entry. These controls matter when contractors finish projects, visitors leave, and employees switch roles.
How to use QR Codes for authentication more confidently
A great QR authentication program starts with the journey, not the code. Teams need to know who will scan, where the scan happens, what device the user has, and what success looks like.
Map the user journey before building the flow
Start with the moment the QR Code appears. Does the user see it on a laptop, kiosk, badge reader, sign, or check-in screen? Does the scan open a browser, mobile app, or approval prompt? Then map the next few seconds so the user understands what they will approve and how the system confirms success.
Keep messaging simple and specific
Clear call-to-action copy builds trust. Tell users exactly what the scan does and what comes next. Use prompts like “Scan to approve this laptop login” or “Scan to confirm your visitor check-in.” Avoid vague instructions like “Scan here” when the scan controls access. Specific messaging helps people stop when a prompt and destination do not match.
Build in fallback and accessibility options
Not every user can scan every time. Phones run out of battery power. Cameras break. Network connections fail. Some users need accessibility support. A confident QR Code authentication strategy includes backup codes, assisted check-in, hardware keys, email approval, or admin support. Fallbacks should match the same risk level and keep access moving safely.
Make authentication simpler and safer
QR Codes for authentication help businesses deliver access that feels fast, clear, secure, and user-friendly. They connect screens, devices, and users naturally while teams add robust controls behind the scenes.
The best flows reduce typing, waiting, and support tickets while adding expiration, session matching, device checks, and approval prompts. They help SaaS teams polish login, enterprise teams manage shared devices, and frontline teams move quickly without cutting corners. When the scan seems clear, and the controls stay strong, authentication starts to feel like part of the product experience.
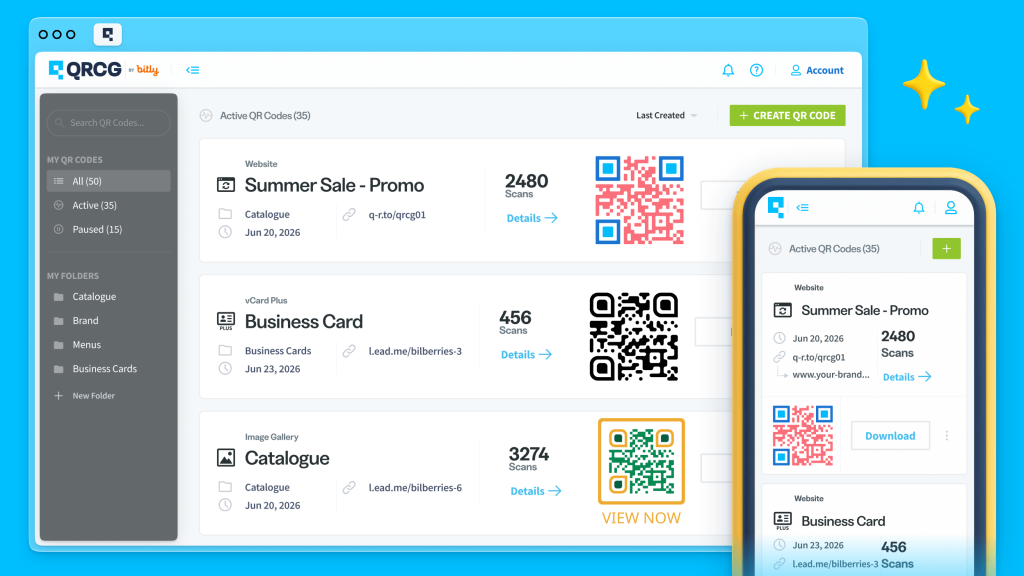
QR Code Generator gives teams a practical way to create and manage QR Code experiences with more confidence. For authentication-adjacent workflows, Dynamic QR Codes can help teams build time-sensitive access journeys and update destinations when workflows change.
Ready to start building your secure QR Code-based login solution? Sign up for QR Code Generator today and shape access moments that feel simple from the first scan.
FAQs
Are QR Codes used for authentication secure?
They can be secure when the system behind them includes strong protections such as dynamic codes, short expiration windows, trusted-device checks, and secure destinations. The QR Code itself is not the security feature. What matters most is how the authentication flow verifies identity and manages the session.
Can QR Codes be used for two-factor authentication?
Yes. QR Codes can support two-factor authentication by adding a second verification step after the initial login. For example, a user might sign in on one device and then scan a QR Code with a trusted phone to approve the session. This can make 2FA feel faster and easier to complete.
Is QR Code authentication the same as passwordless login?
Not always. QR Code authentication can be part of a passwordless login flow, but it can also work alongside passwords or other verification methods. In some systems, the scan replaces password entry. In others, it simply helps confirm identity in a more convenient, cross-device way.
Where do QR Codes for authentication work best?
They often work well in enterprise and SaaS settings where speed and convenience matter, such as shared device access, cross-device login, visitor check-in, kiosk authentication, and identity confirmation. The best use cases are the ones where scanning reduces friction while still supporting a trustworthy verification process.
What should businesses consider before implementing QR Code authentication?
Businesses should review the full user experience, including accessibility, device access, fallback options, session controls, and post-scan clarity. It also helps to define the goal early, whether that is a smoother login, stronger 2FA, or faster identity verification, so the workflow stays focused and easy to trust.