- Best Practices ●
- COVID-19 ●
- Industry Trends ●
- Partners ●
- Product ●
Quishing & QR Code Security: A Guide to QR Code Safety
You likely see QR Codes everywhere. Restaurants use them for menus. Marketers use them for campaigns. Cities use them for parking. These codes have become an essential part of our mobile-first world. However, this popularity attracts attention from bad actors. We have seen a significant rise in a specific type of cyber threat that takes advantage of how QR Codes work over the past year.
Security experts call this threat “quishing.” It targets the trust users place in these black-and-white squares. Understanding QR Code security matters more than ever for both consumers and enterprise businesses. You need to protect your brand reputation and keep your customers safe.
This guide provides updated definitions, examples of risks, and actionable prevention strategies. We will show you how to identify malicious QR Codes and implement safety measures that secure your marketing campaigns.
Note: The brands and examples discussed below were found during our online research for this article.
-
Table of contents
- What is quishing?
- How quishing works: Common tactics scammers use today
- Quishing vs Phishing: Key differences to know
- The risk of quishing and other QR Code security threats
- How to spot quishing attempts and suspicious QR Codes
- Best practices for QR Code security
- What to do if your brand is a quishing target
- Strengthen QR Code security with QR Code Generator PRO
What is quishing?
Quishing involves cybercriminals using modified QR Codes to execute phishing attacks. The term combines “QR” and “phishing.” Instead of sending malicious links via text or email, scammers embed them inside a QR Code.
This technique relates closely to traditional phishing, but it exploits the unique nature of the mobile device. We use our phones to scan codes quickly, often while on the go. This behavior creates a vulnerability.
You must understand the broader context; quishing attacks target mobile-first workflows and contactless payments because public use of these technologies is so widespread. Hackers know that people scan codes to make payments or view restaurant menus without thinking twice. You may be wondering, “Do screenshots of QR Codes work for quishing attempts?” Unfortunately, if users scan them without paying attention, they often will.
How quishing works: Common tactics scammers use today
Scammers use deceptive tactics to trick unsuspecting victims. A common method involves QR Code overlays. Criminals print stickers with fake QR Codes and place them over legitimate QR Codes. You might see this tactic used to attack QR Code parking systems or transit posters.
Attackers also use digital methods. They may create phishing emails that contain a QR Code instead of a link. Secure email gateways often fail to detect these images as malicious, allowing the email to reach your inbox. Once you scan the code, it directs you to a fake website that looks exactly like the real login portals for Microsoft or another major service.
These tactics exploit user trust in physical placements and branding. Another evolving threat involves business invoice spoofing. In this scheme, a scammer sends a fake bill with a QR Code for “easy payment,” directing funds to a fraudulent account.
Quishing vs Phishing: Key differences to know
You need to distinguish between these two threats to fight them effectively. Phishing typically arrives via email or text. Quishing relies on the visual scanning QR Codes process.
Traditional phishing often allows you to hover over a link to see the destination. Quishing removes this safety check. You cannot easily see the URL before you scan the code. This makes social engineering attack vectors harder to spot.
Quishing is gaining popularity as other phishing variants recede because it effectively targets mobile devices. Mobile screens are smaller, and URLs are hidden as part of the process. Users are also more distracted when using a phone, as compared to a desktop computer.
Here are the key differences between phishing and quishing to remember:
- Delivery Mechanism: Traditional phishing typically arrives via text messages or emails containing links. Quishing uses a QR Code, either digital or physical, to deliver the malicious link.
- Link Visibility: In traditional phishing, users can often hover over a link to preview the destination URL before clicking. Quishing removes this safety check, as the URL hides behind the visual code and cannot be easily seen before scanning.
- Target Device: Quishing specifically targets mobile devices because users require them to scan the codes, whereas phishing targets a broader range of devices.
- Detection by Security Tools: Secure email gateways often fail to detect malicious images (like QR Codes), allowing quishing emails to reach inboxes more easily than traditional text-based phishing links.
- User Context: Quishing exploits the distracted nature of mobile usage, where screen sizes are smaller, and URLs are often hidden to save space.
- Method of Interaction: Quishing relies on the visual process of scanning a code, while phishing relies on the user clicking a text-based link.
The risk of quishing and other QR Code security threats
The dangers extend far beyond simple data theft. Quishing opens the door to severe cybersecurity breaches.
One primary risk is credential harvesting. In this scheme, a user scans a code and lands on a fake login page. They enter their login credentials, and the attacker captures them instantly. This can lead to Business Email Compromise (BEC) if an employee uses their work device.
Other risks include:
- Malware deployment: Scanning a code can trigger a drive-by download that installs malware or spyware on the device.
- Financial fraud: Fake QR Codes can initiate unauthorized payments or steal financial information like credit card numbers.
We also see broader QR Code security concerns beyond phishing. Tampering involves physically altering a code in a public space. Redirect hijacking occurs when an attacker compromises the destination URL of a dynamic code.
These threats can cause operational disruption and supply chain risks for all types of businesses. A compromised code on product packaging or a marketing asset can damage brand trust instantly.
How to spot quishing attempts and suspicious QR Codes
You can protect yourself and your organization by learning to spot the red flags. Vigilance is your best defense against QR Code scams.
Start with a visual inspection. If you scan a code on a poster or table, check for stickers. Does the code look like someone pasted it over the original? If so, do not scan it.
Always validate the URL. Your camera app or scanning app should display a preview of the link. Read the domain carefully. Fraudulent websites often use misspellings or generic domains to spoof legitimate brands.
Use mobile security tools that block malicious sites. Many modern browsers include QR Code preview features that allow you to inspect the link before opening it.
Follow this simple checklist:
- Inspect the physical code for tampering.
- Preview the URL before clicking.
- Check for HTTPS and correct domain spelling.
- Be skeptical of unsolicited codes in emails or other media.
Best practices for QR Code security
Businesses must take proactive steps to ensure QR Code safety. We recommend broadening your prevention advice beyond just quishing to address QR Code security overall.
Regularly provide tips on how to spot and avoid quishing scams. This is crucial if you use QR Codes often, as some people may lower their guard when they come across codes masquerading as yours.
Consistent branding helps users recognize your legitimate codes. Use custom QR Codes that feature your logo and brand colors. Scammers can struggle to accurately replicate the high-quality, branded designs produced by the best QR Code generators.
Secure your digital destinations. Ensure all landing pages use HTTPS and protect sensitive user flows with Multi Factor Authentication (MFA). Never use static URLs for processes that involve sensitive information or payments.
Monitor your public placements for tampering. If you use codes on physical signage, check them regularly. Remove any unauthorized stickers immediately.
If some of your customers have fallen victim to quishing scams, raise awareness by letting your audience know how and where the attacks occurred to reinforce trust and transparency.
Use QR Code management systems with controlled editing and user authentication. These platforms allow you to manage who can change the destination of your codes, preventing unauthorized redirects.
What to do if your brand is a quishing target
Discovering that scammers are using your brand for a quishing campaign requires immediate action. You must mitigate the crisis quickly.
Notify your users immediately. Use your official social media channels, email newsletters, and website banners to alert customers. Tell them exactly what the fake QR Codes look like and where they might appear.
If fake codes appear in public places, take physical action. Send teams to remove stickers from your signage or parking meters.
Coordinate with your cybersecurity teams or law enforcement. Report malicious websites to Google Safe Browsing and the FTC. This helps get the fraudulent sites taken down faster.
If the attack involves a compromised Dynamic QR Code, update the URL immediately. Redirect the traffic to a warning page that informs users about the security issue.
Always scan your codes to confirm they direct audiences to the right destinations. Regular testing can help you identify when scammers replace legitimate QR Codes with fake ones.
Strengthen QR Code security with QR Code Generator PRO
Quishing and security threats are critical issues, but they should not stop you from using this powerful technology. You simply need the right tools to stay safe.
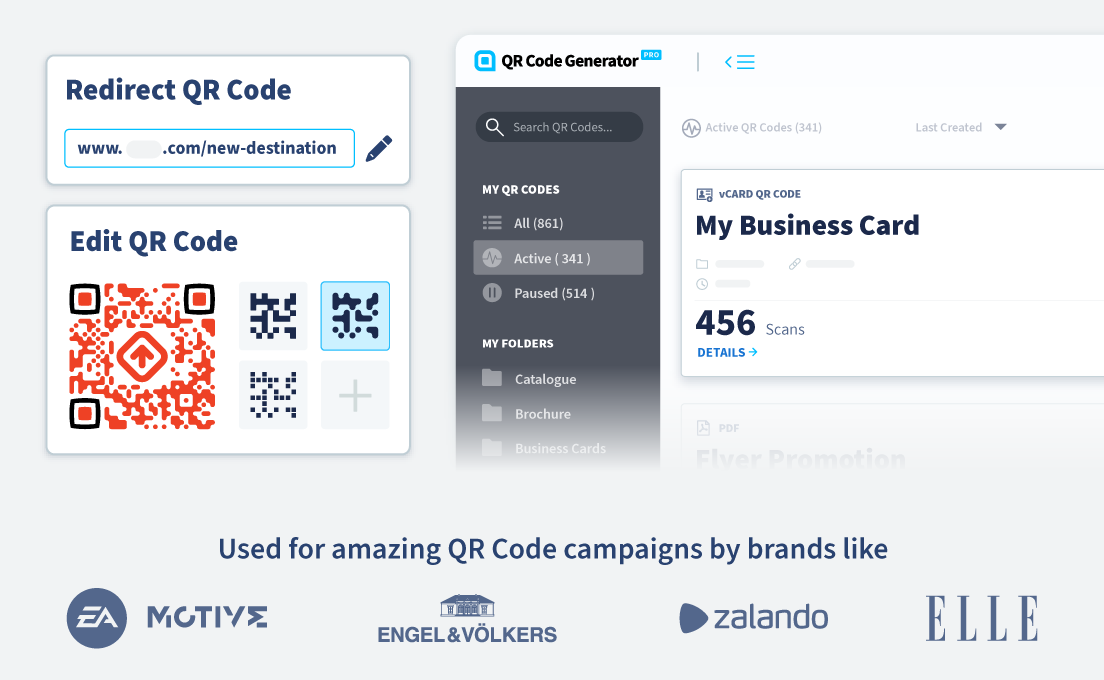
QR Code Generator PRO offers features specifically designed to enhance security and trust. Custom branding allows you to create tamper-resistant visual identities. When your code includes your logo and specific design elements, it becomes much harder for a scammer to paste a generic sticker over it without users noticing.
Our platform provides Dynamic QR Codes with editable, trackable URLs. This setup gives you control. You can update the destination if a link breaks or becomes unsafe, and have access to centralized management of your campaigns. This visibility allows you to monitor scan data for unusual activity, and you can retire or update codes instantly. If a campaign ends, you can redirect its codes to a safe landing page or deactivate them.
Ready to secure your campaigns? Sign up for QR Code Generator PRO and start creating safe, branded codes today.




 Add custom colors, logos and frames.
Add custom colors, logos and frames.
